Minimum Baseline of Cybersecurity for Municipalities
Goal 3: Cyber Incident Response Planning
 Benefits - Create effective strategy for handling cybersecurity incidents; minimize incident impacts; strengthen municipal defenses against future incidents; and help municipalities to understand their cybersecurity environment, identify risks and gaps, and create effective protection and response strategies.
Benefits - Create effective strategy for handling cybersecurity incidents; minimize incident impacts; strengthen municipal defenses against future incidents; and help municipalities to understand their cybersecurity environment, identify risks and gaps, and create effective protection and response strategies.
How - Create a plan by utilizing resources/tools to identify data, systems, and technical infrastructure in order to protect against cyber attacks, and possible actions to take for recovery if a cyber attack occurs.
Download the Informational PDF 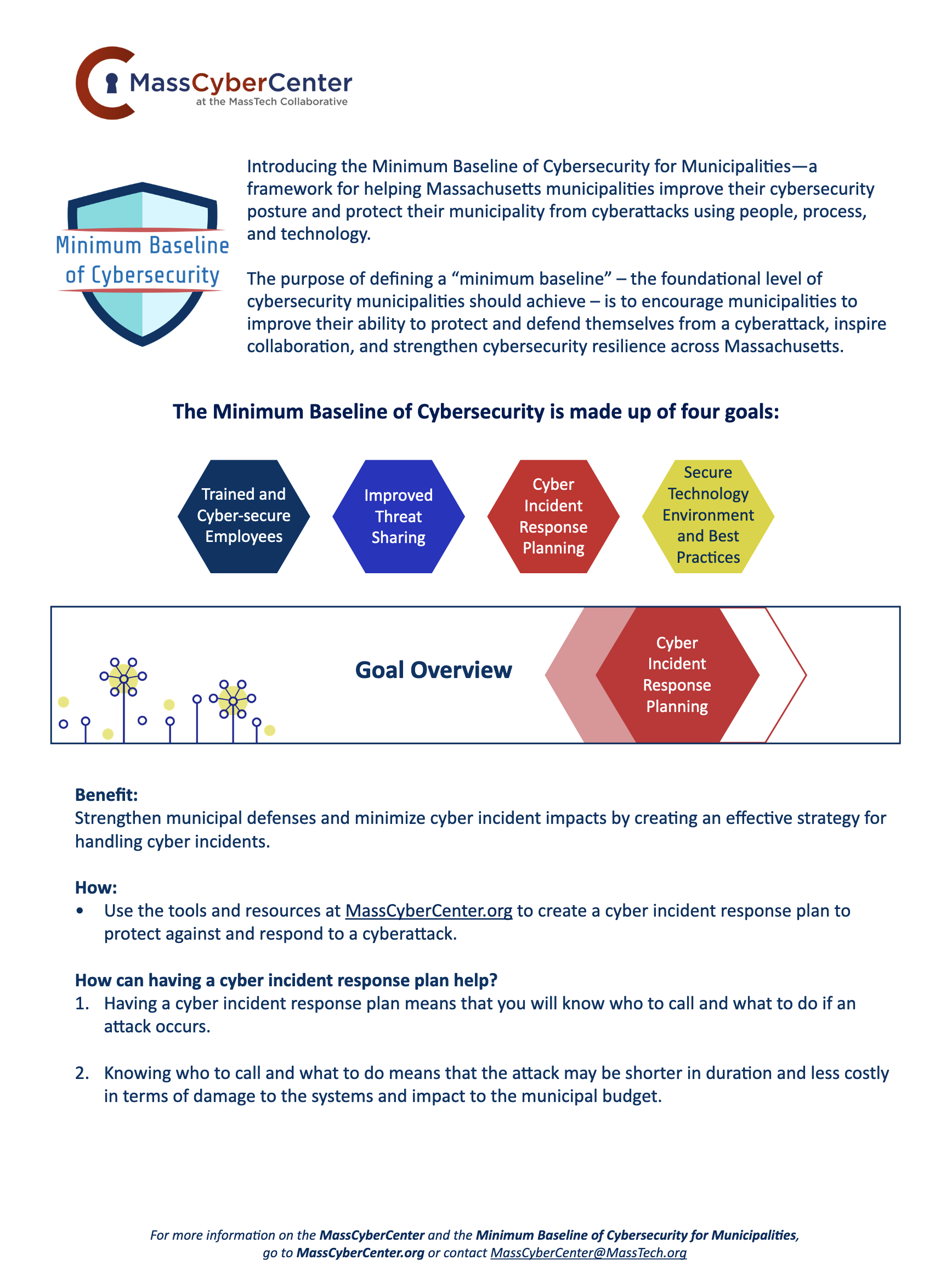
Watch the Learning Module Below to Learn More
Resources
| Item/Document | Description | Link | Access |
|---|---|---|---|
|
MassCyberCenter
|
Materials from the Cyber Incident Response Plan Workshops for Municipalities which explain the value of cyber incident response plans, provide self-assessment and planning guidance, and give municipalities the tools and resources they need to create a cyber incident response plan | https://masscybercenter.org/response-plan-materials | All |
| SANS Institute Incident Handler’s Handbook | SANS Institute document that concisely describes a six-step incident handling process and includes a handy incident handler’s checklist for each of the steps (i.e. preparation, identification, containment, system -backup, eradication, recovery, and lessons learned) | https://www.sans.org/reading-room/whitepapers/incident/incident-handlers-handbook-33901 | All |
| National Institute of Standards and Technology (NIST) Computer Security Incident Handling Guide | Provides information on how to prepare, identify, protect, detect, respond, and recover from a cybersecurity incident. Includes examples and checklists | https://nvlpubs.nist.gov/nistpubs/SpecialPublications/ NIST.SP.800-61r2.pdf |
All |
| Operational Services Division at the Massachusetts Executive Office of Administration and Financial – ITS78: Statewide Contract for Data, Cybersecurity, and Related Audit, Compliance, and Incident Responses Services | State-wide contract for vendor services, including a full range of audit, penetration tests, reviews, and validation of compliance with legal, regulatory and policy requirements, and related services in areas such as data breach investigation, remediation, and security of confidential information | https://www.mass.gov/doc/its78/download | All |
